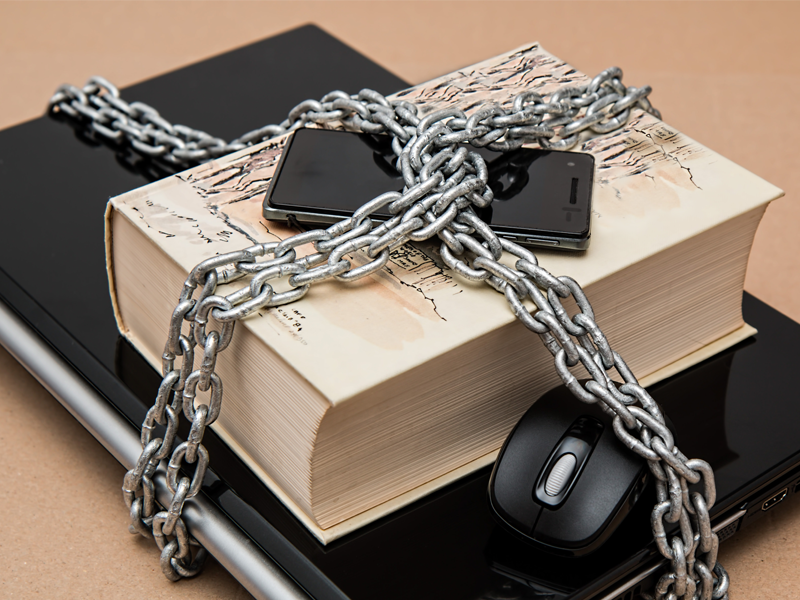
During the last decade, social media has evolved and revolutionized not only the way we communicate with each other, but also the way we live. In almost every case, social media such as Facebook, Twitter, YouTube, Google+, and Instagram have found a way to embed themselves into our daily lives. So what does this all really mean? It means that through the development and advancements of technology, we have developed a new dimension in which we partially live in. Many fail to realize that security is just as important online as it is in real life and thus importance of the safety of your identity with social media.
With more and more integration and merging of social media, it is becoming almost too easy to become a victim of identity theft. On average, it is only a matter of a few minutes to track a person’s social media account via Google’s search engine, and thanks to the integration of for example, Instagram to Facebook, or Google+ to YouTube and so on, it is a matter of just a few more minutes to gather a person’s full online social accounts.
Everything you’ve read should be of no surprise. Where in all of this do you become vulnerable and exposed to the compromise of your identity? Ask yourself, in any given year, how often you dispose of your credit card statements or bank statements without the use of a shredder or at least ripping it apart completely? How many times do you leave your ID, credit card, bank card, or any other personal information in the car or somewhere in the open? How many times do you purchase something online? If your answer to those questions made you feel confident that this read may not apply to you, then answer this: How many times do you hand over credit card to a waiter/waitress to process your bill away from your sight?
These examples (among many others) are opportunities that could lead to the compromise of not only your money, but also your identity. With the advancements and convenience of social media, many fraudsters and scammers have also learned and advanced their techniques as well. Surely, with only a credit card number, your name, and the pre-existing liability insurance on your credit card you wouldn’t have to worry, right? Wrong. Criminals skilled in fraud have learnt that metaphorically, a slice from a pie is not as good as 2 or 3 whole pies.
With patience and some digging around, it is through the use of social media that your current location (address), birthday (DOB), name of pets and relatives (answers to secret questions), your current and previous employers, and your phone number could be determined. With that information alone, the right vocal cords, and an inexperienced agent in a call centre, a fraudster could request a credit bureau pull on you and apply for multiple lines of credit destroying your credit for nearly a decade. That being an extreme case, the fraudster could call your bank, get completely verified with the mentioned personal information, and request credit limit increases, inquire about available credit, request to reset your online banking for money transfer, or get a new plastic card issued to their address if they don’t already have it in their hand.
Just as we protect our personal information in real life, it is even more important to protect it online. Although the exchange of information is one of the best and main features of social media, it is vital to be conscious of the information being exchanged and exposed.
To conclude, although it is becoming more and more valuable to have an online footprint, it is important to be aware of what you are associating with your identity. Would you believe it?
If I told you one of the tools used by bank fraud investigators to validate an identity for loan approvals is through the use of social media? Since a first time applicant applying online or via phone is virtually non-existent in credit bureaus, when in doubt, bank investigators use these same tactics to help determine if indeed the information given connects to a real person by finding their online profile.
This is a guest blog post by Fanny Anon.

![Give Your Audience a New Perspective With UGC + DAM Webinar with Widen [Summary, Slides, and Recording]](https://www.tintup.com/blog/wp-content/uploads/Screen-Shot-2018-09-14-at-1.52.14-PM.png)